Change Cid Sd Card
I am trying to copy-protect some work, which is a bootable SD card booting a Linux kernel on ARM device (Raspberry Pi). I am using this approach:
Some also call this “reading the PSN off the SD card” or reading the product serial number off the SD card. Most phones and much of the software on phones will lock in to the CID number of a SD card. The CID number is a unique card identifier number that is unique to the card itself. China 8GB 16GB Change CID SD Card IOKZ077-#7124 is supplied by ☆ 8GB 16GB Change CID SD Card manufacturers, producers, suppliers on Global.
- The approach uses an initrd to mount an encrypted root filesystem.
- The initrd generates the filesystems' password according to the CID of the SD card. (a hash function is used, did not decide yet over md5 or sha1). Initrd will try to mount the filesystem using that generated password.
- Now here is the most interesting/suspect part: The initrd itself is encrypted using a custom C function, basically each byte is XOR'ed using a custom made pseudo random generator.Kernel is modified to have the same encrypting function, which works as decryptor.
- The system itself is stripped down so there is no way to use a keyboard or external storage. A single app runs full-screen.
So after the bootloader loads kernel and initrd, the kernel decrypts the initrd and executes its init script, which will generate the password and mount the root filesystem.
My question is: How easy it would be to break this setup (to decrypt the root filesystem and make it boot from any SD card)? What are the most weakest parts? How easy is to decompile the kernel and find those custom encrypting functions?
EDIT: Here are some corrections so you don't waste time with the obvious things:
- The root device will be encrypted with LUKS (aes256) and the key will be generated by some HMAC function using SD card's CID and some salt.
- The pseudo random algorithm for initramfs encrypting will be in fact RC4, just the key will be generated using some custom function, because if I just store the key in a byte array it makes it dead simple to retrieve it (yeah this is security through obscurity but there seem no other way).
- I understand that if using a SD card emulator someone can make a copy of this system start but this is OK with me, because its pretty difficult and not anyone can do this.(also not anyone will want to deal with emulators)
closed as too localized by Keltari, David Schwartz, Journeyman Geek♦, Ƭᴇcʜιᴇ007, Tanner FaulknerMay 28 '13 at 18:03
This question is unlikely to help any future visitors; it is only relevant to a small geographic area, a specific moment in time, or an extraordinarily narrow situation that is not generally applicable to the worldwide audience of the internet. For help making this question more broadly applicable, visit the help center. If this question can be reworded to fit the rules in the help center, please edit the question.
2 Answers
How easy it would be to break this setup (to decrypt the root filesystem and make it boot from any sd card)?
How hard it is to 'break' your setup depends on the number of bits of entropy in whatever method you're using to sign/encrypt the filesystem itself (as this determines the total number of unique combinations that can be used to brute-force the password).
What are the most weakest parts?
Without a doubt, using a predefined CID as a password, as well as using a custom pseudo-random number generation function.
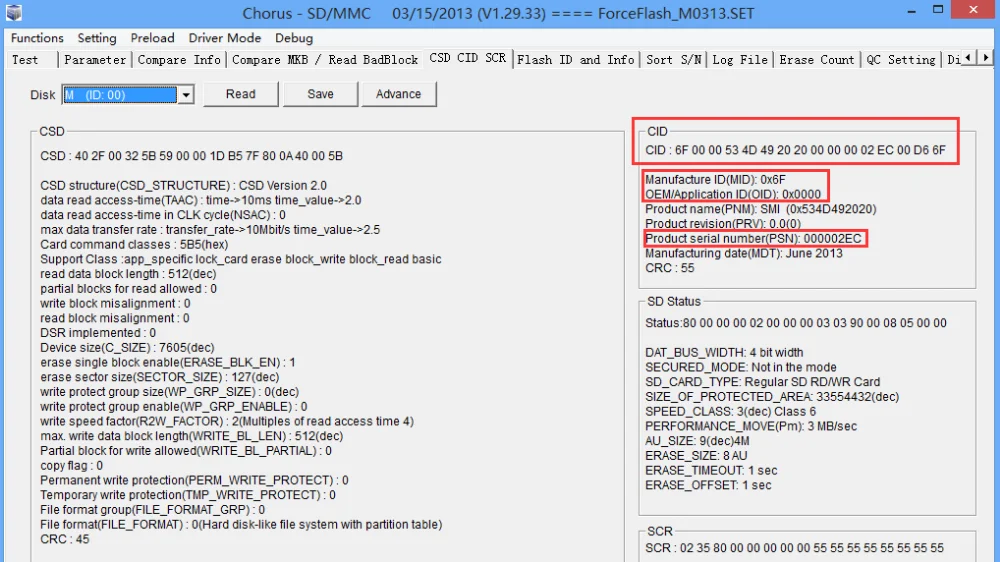

The CID of an SD card is only supposed to be read-only, but it's not uncommon to find non-compliant flash memory devices in this day and age. Some people have even demonstrated the ability to overwrite the CID with certain SD cards. This would make it easier to brute-force the password, especially if one is just emulating an SD card after cloning yours (which is something else you might want to consider).
Finally, using any kind of pseudo-random number generator already has some intrinsic flaws, precisely because it's not random - there is a reason it's called pseudo-random. It might be better to use a pre-made encrypted bootloader (like TrueCrypt or LUKS, which both work on the Raspberry Pi) and avoid having to make any manual kernel modifications.
How easy is to decompile the kernel and find those custom encrypting functions?
It's very difficult to decompile anything. Conversely, de-assembly of a compiled application is often trivial, and there are many tools which can be used to assist with reverse engineering assembly back into another higher-level language. If an attacker has access even to a compiled kernel, analyzing something like a pseudo-random number generator is probably trivial unless the code is obfuscated on purpose.
TL,DR: Don't re-invent the wheel when it comes to encryption and security, stick with the tried and true. There are several full-disk encryption options that are already available and have been demonstrated to work just fine on the Raspberry Pi. I would avoid using the CID of the SD card as a kind of 'password' - even if it cannot be changed, there are ways to spoof this value. Veer zaara mp3 download.
Copy protection is already included in the SD card specification as CPRM.
Credit Card Cid Number
Someone skilled wouldn't have much trouble cracking this. It'd be relatively easy to boot the SD card under an emulator, and then just read the keys out of RAM. Then they post a version without the copy protection to the Pirate Bay (etc.), and that's that.
Alternatively, use the emulator to inject shellcode into the running emulated system. Then use the running system to copy the decrypted rootfs off (or read the keys using dmsetup table --showkeys, etc.)
A quick search turns up the existence of Raspberry Pi emulators, so part of the work has already been done.
You've got another problem, in particular this:
Kernel is modified to have the same encrypting function, which works as decryptor.
Anyone you distribute this to is entitled to the kernel source code, under the terms of the GPL. So you wouldn't need to disassemble it, you could just use diff to find the extra function.
(Not that finding it through disassembly would be that hard, as you can e.g., check vs. a stock kernel)
Sd Card Formatter
I'm not completely familiar with the Raspberry Pi boot code, but if you can reflash the bootloader with an embedded crypto key (that is then passed to the kernel), that'd at least not be on the SD card, so it'd foil an attempt to get it to boot in an emulator.